

As networks become more complex and distributed, seeing and responding to threats has become increasingly difficult.
This has led to a security sprawl that complicates management, fragments visibility, and limits the ability of organisations to respond effectively to threats. That’s due, in part, to today’s enterprises having deployed an average of 45 security solutions across their network, making any sort of centralised management nearly impossible.
And worse, detecting and responding to a cyber incident requires coordination across 19 of those tools, leading to complex workarounds that need to be constantly managed and reconfigured every time a device is upgraded.
Despite these challenges, it is still all too common for organizations to move first and ask how best to secure and manage changes to their networks later—creating a perfect storm for attackers and threats looking to exploit silos, complexities, and visibility gaps that naturally arise from such complex and piecemeal environments. So, it should come as no surprise that Cybersecurity Mesh Architecture (CSMA) by Gartner—an integrated set of security tools and APIs combined with centralised management, analytics, and threat intelligence—made it onto their list of top cybersecurity trends for 2022.
Cybersecurity mesh platform: What is it?
Today’s enterprises aren’t just looking for a unifying architecture that can bring their fragmented infrastructure and deployments under control.
They need a system that makes deploying new technologies and services secure and straightforward. This requires more than workarounds connecting disparate security technologies.
They need a broad, integrated, and automated cybersecurity mesh platform that provides centralised management and visibility, supports and interoperates across a vast ecosystem of solutions, and automatically adapts to dynamic changes in the network.
While Gartner calls this idea a “Cybersecurity Mesh Architecture,” for more than a decade we have called it the “Fortinet Security Fabric.”
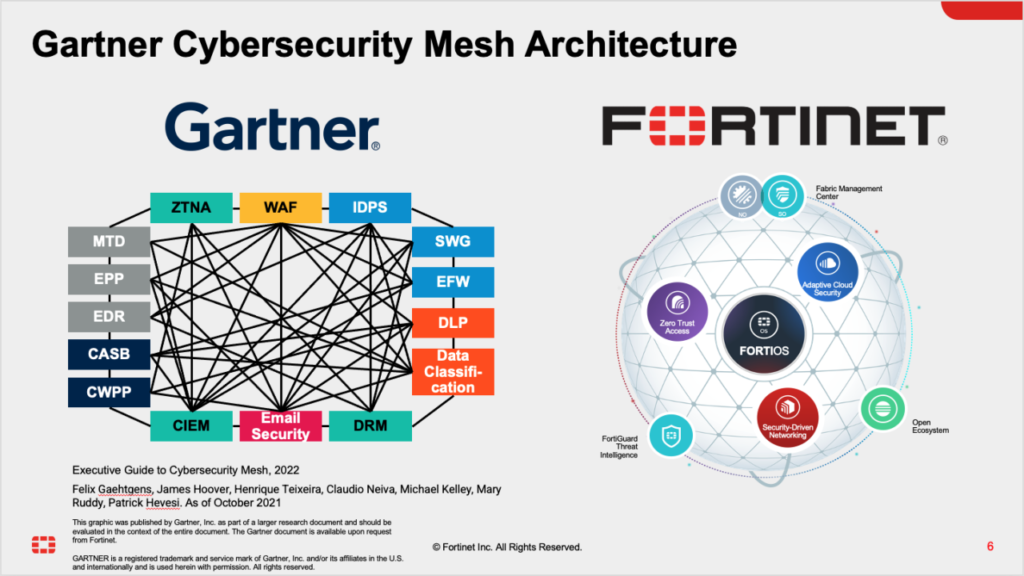
Fortinet spearheaded the doctrine that a broad, integrated, and automated cybersecurity mesh platform is essential to reducing complexity and increasing overall security effectiveness across today’s expanding networks. New and increasingly complex trends, like work-from-anywhere (WFA), are the perfect use cases for a unified security mesh architecture. WFA requires multiple solutions to work together across a dynamic set of campus and data centre assets, distributed home offices, and cloud-based applications.
The Fortinet Security Fabric is ideally suited to address these new complex challenges. Our portfolio of more than 50 security and networking technologies—the largest in the industry—are designed from the ground up to interoperate—sharing threat intelligence, correlating data, and automatically responding to threats as a single, coordinated system.
What’s more, Fortinet is delivering on the convergences of not just cybersecurity products, but the convergence of security and networking – what we like to call “security-driven networking” – by delivering industry-first innovations such as Secure SD-WAN.
We also believe that a true cybersecurity mesh platform should further break down technology and vendor silos by enabling and supporting a broad open ecosystem of technology partners. To this point, we currently integrate and interoperate with over 450+ third-party technology partners as part of our Fortinet Security Fabric open ecosystem. Such an open ecosystem matters because it empowers organisations with flexibility across their deployments while benefitting from consolidated and converged operations, visibility, and security. It also preserves existing investments in technologies and solutions until they are ready to move towards an even more integrated and automated Security Fabric experience.
Such an approach is not just suitable for enterprises. Channel partners can provide their customers with a more robust solution—and make more money—with a mesh platform strategy than simply selling point products. A broad portfolio of genuinely integrated solutions allows them to add real value by applying their expertise and architectural capabilities to solve the more considerable challenges today’s organizations face.
The trend towards a more unified approach to security is inevitable, whether to secure emerging network security challenges like WFA, to combat the increasing threat of ransomware, or to reduce the overhead of managing a sprawling set of isolated security solutions.
In fact, Gartner believes that “by 2024, organisations adopting a cybersecurity mesh architecture to integrate security tools to work as a collaborative ecosystem will reduce the financial impact of individual security incidents by an average of 90 per cent.”
What to expect from the industry’s highest-performing cybersecurity mesh platform

The great news for Fortinet’s customers is that they don’t have to wait until 2024 for the industry to deliver a new cybersecurity mesh architecture – they can reap those benefits today with the Fortinet Security Fabric. Those benefits include:
- Deep visibility across all edges
- Centrally managing distributed solutions
- Consistent enforcement of policies
- Leveraging anonymized threat intelligence provided by Fortinet Security Fabric customers around the world
- Third-party integrations for improved protection against known and unknown attacks
- Automating actionable responses across hybrid environments.
William Shakespeare once wrote, “a rose by any other name would smell as sweet.”
So, too, is a broad, integrated, and automated cybersecurity mesh platform. Whether one wants to call it a “cybersecurity mesh architecture,” a “cybersecurity platform,” or “Fortinet Security Fabric,” the results are the same.
The important thing is that organizations embrace and adopt an integrated approach to security as part of their digital acceleration initiatives. This will provide them with reduced complexity, simplified operations, and greater security effectiveness regardless of where their journey takes them.
—Article by John Maddison, EVP of Products and CMO at Fortinet







Comments